
Every small business needs BDR – backup and disaster recovery – to protect their business from risk. A managed services provider can help.

Every small business needs BDR – backup and disaster recovery – to protect their business from risk. A managed services provider can help.

Unless you plan to shutter your doors when the next disaster strikes, you need to have BDR in place. Take action now.
Security, scalability, and accessibility are three primary benefits of offsite replication through thinkCSC’s public cloud backups.

Paying the ransom when your organization is struck with ransomware does not guarantee access to your data. Proactive measures are necessary.
Baltimore is the latest city government to fall victim to ransomware, for the second time in as many years. The city’s systems have been locked up since May 7 after being attacked by “RobbinHood” ransomware.
While the mayor is refusing to negotiate with the hackers or pay the 13-bitcoin ransom they’ve demanded, many of the city’s networks have been compromised, including police email and board of elections.
What Is RobbinHood Ransomware?
RobbinHood ransomware is a ransomware that targets an entire network and attempts to take over as many systems as possible. Once infected with the ransomware, it demands bitcoin payment in order to release the files. In the case of Baltimore, they’ve requested demanded $17,600 in bitcoin per system — a total of about $76,280, according to Dark Reading.
How Do You Get RobbinHood Ransomware?
Like other ransomware, the RobbinHood hackers gain access to an organization’s network through phishing emails that are deliberately designed to appear legitimate to the recipient of the email. In the case of Robbin Hood, they use several psychological tricks to compel the email recipient to click on the link that begins the encryption process. Prior to the attack on Baltimore, they successfully infiltrated Greenville, North Carolina networks.
Stop Clicking Links and Downloading Files
Email is a convenient method for communicating and has made business operations so much more efficient, but every employee in every organization has an obligation to stop clicking on links and files. If there is any doubt whatsoever about the legitimacy of the email (and even if there is not any doubt) follow up in person or over the phone with the sender to make sure they actually sent the file.
What to Do If You Get Ransomware
If you believe your network has been infected with ransomware, or if you have received a ransom demand, immediately disconnect from the network and call your IT department or managed services provider. In many cases, you can prevent the attack from getting worse by removing access to the network by the infected system.
Don’t Pay the Ransom
Paying the ransom only fuels the motivation of hackers to continue holding businesses hostage. Instead, make sure you have mitigated your risk by having a disaster recovery and data backup plan in place. Regular offsite backups can protect you from needing to pay a ransom to gain access to your network.
If you are concerned about the threat of RobbinHood and other common ransomware threats, contact us to learn more about how you can improve your security and better protect your organization. As you can see, every organization – from schools and hospitals to municipalities and utilities to businesses of every size – are at risk.
At thinkCSC, we take security seriously, offering innovative levels of security monitoring for our clients. Cyber threats are a normal part of doing business, but these risks can, and should, be addressed and abated. Partnering with the right managed services provider does make a difference. Today’s MSP does more than just provide technology and facilitate server upgrades; the right MSP is an integral layer of your cybersecurity, providing the expertise you need to remain competitive, secure, and in business. We can partner with your Columbus-region organization to develop a unique solution designed to fit your business model. Take the first step towards advanced cybersecurity practices and contact us today to learn more about our managed security services.

Ransomware happens, often with a momentary lapse of vigilance on the part of an employee or third-party vendor, but you can fight back.

Schools must take cybersecurity seriously with layered security, network access control, training, and early threat detection for edtech.
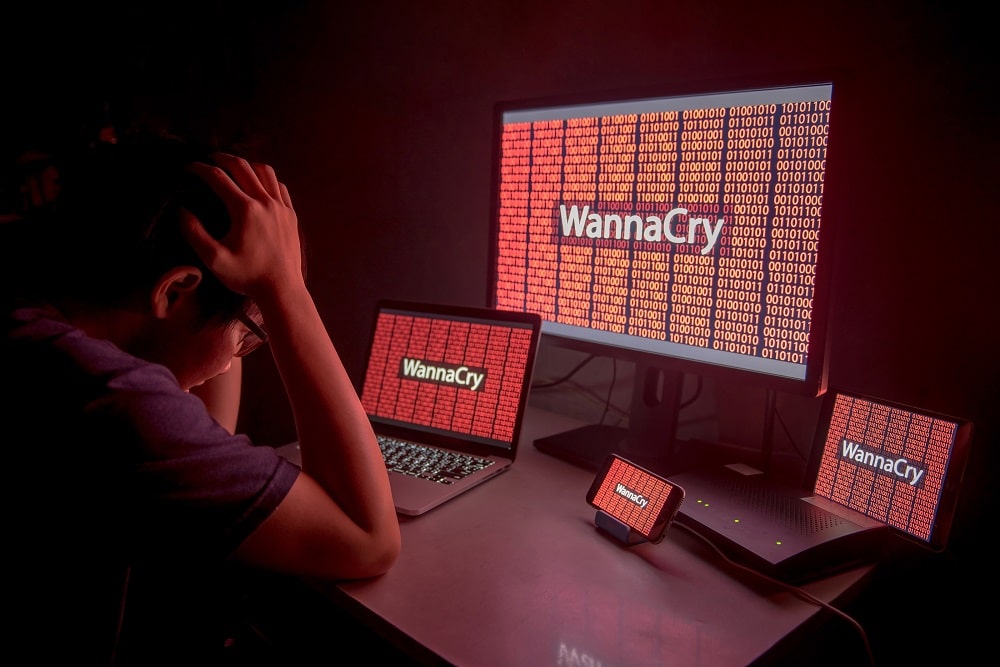
thinkCSC has been closely tracking a global ransomware attack called “WannaCry” and all thinkCSC managed services clients are safe.

In the world of technology, proactive adopters have a huge advantage over those who wait to implement a new technology until it has been fully tested. Proactively navigating the rapidly changing world of technology has historically been most difficult for small and medium-sized businesses (SMBs). Due to the traditional cost and complexity of technology, these businesses have struggled with early adoption of cutting-edge technologies. This has allowed larger companies to dominate the first wave of benefits from emerging innovation, while smaller companies have played catch-up – or even settled for second-generation systems on a regularly revolving schedule as first-generation systems are developed.
Now, due to a much more robust, competitive market within technological innovation, as well as the ability to partner with experts in the effort to implement and stay on top of new systems, SMBs can compete on nearly-equal footing with large enterprises. Whether this occurs or not depends entirely on whether SMB owners and leaders understand and capitalize on the three areas in which technology is changing the way business is conducted: the cloud, mobility, and security. In part one of this two-part series, we’ll explore the benefits of cloud services for SMBs.
Everything as a Service: Doing Business in the Cloud
The central benefit of using cloud services is cost-effectiveness. It is the relatively low cost of cloud-based datastorage, cloud-based applications and software, and cloud-based security measures that truly level the playing field for SMBs. Implementing cloud-based services can minimize the economic impact to your IT budget by guaranteeing a predictable monthly cost and uptime for your IT environment. A managed service provider (MSP) converts your organization’s IT spend from a capital expenditure to a predictable and manageable monthly operating expense, much like a utility.
Cloud services can be tailored to specific requirements, especially where compliance may be an issue – and more and more, compliance is an issue affecting businesses of all sizes:
While compliance is something larger enterprises implement as a matter of course, smaller businesses may only begin to consider these requirements as they grow (or after they’re fined for non-compliance). When choosing cloud services, security is one of the most important considerations. You need to know where your data is stored and who has access to it, accounting for both digital security and physical security. An IT partner who focuses on maximizing the benefits of your cloud services, which scale to your need. If you store highly-sensitive or valuable information, this option is a much better fit than the public cloud and the only option for businesses of any size who require secure operations.
Understanding and implementing solid cloud, mobile, and security systems has the potential to even the playing field for SMBs. Successfully carrying out this integrated approach can help you grow beyond the traditional constraints of your industry, taking you to places you never imagined you could go. In these areas, thinkCSC has the expertise and experience to help your organization compete effectively in our evolving technological world.

We have all seen ransomware become more sophisticated, regardless of where we live or work. And the cyber assaults seem to be never ending. Just as security and protocols are developed to keep your network secure, hackers use ransomware to go after educational institutions. As colleges and high schools work quickly to develop offsite backup and recovery solutions to protect them from having to pay ransoms in order to access their data, government offices became the target.
Even as technology has made us more efficient and more capable, it has also made us more vulnerable when we don’t implement the right solutions to protect our homes and businesses from these types of attacks. And the biggest threat from ransomware is yet to come: infrastructure threats.
Consider what has happened so far:
It’s likely that the next threat will be even more insidious, as hackers develop methods for compromising entire systems. Georgia Institute of Technology, recognizing the risk to programmable logic controllers (PLCs), developed ransomware with which they could take control of a simulated water treatment plant, gaining access to PLCs to control valves and additives, and even create false readings. While this was a simulation designed to help understand how to prevent an attack, the risk is real.
Businesses of all sizes and in all industries, government entities, schools K-16 and beyond, and individuals must all do their part to prevent ransomware. We must become far more selective about the emails we open, read, and forward, giving special attention to the links we click and the attachments we open. We must invest heavily in better security, from virus software to endpoint detection. We must all take steps to thwart hackers.
At thinkCSC, we believe that in order to achieve maximum success, regardless of the size or type of organization, you must make IT an integral part of your overall business strategy and partner with IT professionals who not only understand how to leverage technology to their advantage but who are also committed to understanding your business goals and aligning your IT strategy to them. We pride ourselves on having the best business-savvy technical experts in the industry. If you would like to learn how to create an IT security strategy aligned with your organizational goals, contact thinkCSC for more information.
Recent Comments